Guide for Firewall configuration in MikroTik RouterOS
- MLE-005 [ cód. 18005 ]
Don’t wait to be vulnerable. Learn how to configure a robust firewall with MikroTik RouterOS and keep your data and devices safe. Access the tutorial now!
- Share the information about this course
Content and access to the Tutorial
Estado actual
Precio
Primeros pasos
Contenido del Curso
This tutorial includes
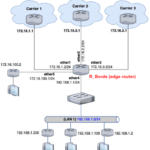
- Logical diagrams of the networks analyzed in the laboratories
- Detailed script of the different configurations
- Permanent access to the training portal
- Access to all future content updates or corrections
What you need to access this tutorial
- Internet connection of at least 1 Mbps
- Laptop or desktop computer preferably
- Tablet or cell phone are an alternative
What the student will learn
By completing this tutorial, students will be able to:
- Basic+Intermediate Firewall Configuration
- Protection against Unauthorized Access
- Management of Vulnerable Services and Ports
- Use of Interface Lists and Address Lists
- Configuration of Rules to Protect Client Traffic
- Implementation of Port Knocking
- Traffic Filtering and Protection against Attacks
- Security in Access to Client Devices
Requirements
- Understand basic networking concepts, such as network types (LAN, WAN), network topologies, and OSI/TCP-IP models.
- Know the differences between public and private IP addresses, and how they are used in networks.
- Have knowledge of subnets, netmasks and IP addressing.
- Understand the basic concepts of routing and switching in networks.
- Know how Dynamic Host Configuration Protocol (DHCP) and Domain Name System (DNS) work.
- Understand the assignment of dynamic and static IPs.
General Objective
The main goal of this tutorial is to train students in the effective configuration of a firewall in MikroTik RouterOS, in order to improve the security of the router and the network.
Participants will learn to configure specific rules for various security needs, from protecting the router to securely managing access to services and protecting client traffic.
Basic and Intermediate Configurations
The advanced general protection firewall rules are explained in detail in the Tutorial (ML-006) Filtering Threats: Firewall Rules to Protect the Router from Common Network Attacks.
This tutorial develops basic and intermediate-level security rules that complement the ML-006 tutorial.
Objectives by Chapter:
1. Configure Input Rules for Router Protection
-
-
- Learn to protect the router from unauthorized access and external attacks.
- Configure rules to allow secure connections and block vulnerable ports.
- Implement measures to disable unnecessary services and efficiently organize interfaces.
-
2. Configure Input Rules to Allow Access to MikroTik Services
-
-
- Understand how to allow specific access to services like VPNs and secure access using Port Knocking.
- Configure the firewall to allow secure access from external networks, using specific port sequences.
-
3. Configure Forward Rules to Protect Client Traffic
-
-
- Configure rules to manage and protect traffic within the network and between different network segments.
- Learn to filter advanced ICMP traffic and block insecure SMTP ports to prevent abuse.
-
4. Configure Access Protection for Client Devices
-
-
- Establish administrator lists to control access to client devices.
- Implement rules to block unauthorized communications between clients and manage secure Internet access.
-
What Students Will Gain Upon Completing this Tutorial
Upon completing this tutorial, students will be able to:
- Configure a firewall in MikroTik RouterOS to protect the router and network from unauthorized access and external attacks.
- Manage secure access to essential services using advanced techniques like Port Knocking.
- Protect client traffic within the network, ensuring secure and efficient communication.
- Implement detailed access management for client devices, ensuring that only authorized users can access specific network resources.
- Apply a comprehensive security configuration that covers everything from router protection to secure management of network traffic.
This knowledge in configuring the MikroTik RouterOS firewall will enable students to strengthen the security of the networks they manage, optimizing protection against a wide range of cyber threats and improving network security management.
-
in RouterOS version 7
$8,99
Need more information?
Get this Tutorial
De nuestro Blog ...
¿Qué es SwitchOS (SwOS) y para qué sirve en switches MikroTik?
Métrica de red: qué es y cómo se usa en el enrutamiento
Cómo crear un Túnel 6to4 en MikroTik RouterOS
You must log in and have started this curso to submit a review.