(Book) Networking with MikroTik RouterOS: A Practical Approach to Understanding and Implementing RouterOS
Study material for the MTCNA Certification Course, updated to RouterOS v7
In MikroTik RouterOS, the “Device mode” is presented as a key feature that sets specific limitations on a device or restricts access to specific configuration options.
At the end of the article you will find a small test that will allow you assess the knowledge acquired in this reading
This article will explore in detail what the “Device mode“, its available modes and how this function contributes to security and customization on MikroTik devices.
MikroTik RouterOS offers two main modes: “enterprise"And"home".
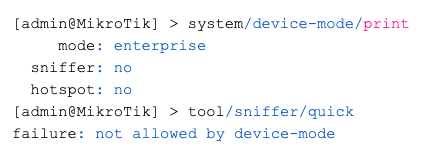
By default, all devices use the “enterprise” mode, which allows all functionalities, except “container”.
El “home” mode disables features such as scheduler, socks, fetch, bandwidth testing, traffic generation, sniffer, romon, proxy, hotspot, email, zerotier and container.
[admin@MikroTik] > system/device-mode/print mode: enterprise
The user can change the “Device mode“, but remote access is not enough to perform this action.
After changing the mode, it must be confirmed by pressing a button on the device or performing a “cold reset” (disconnect the power).
[admin@MikroTik] > system/device-mode/update mode=home
update: please activate by turning power off or pressing reset or mode button
in 5m00s
-- [Q quit|D dump|Cz pause]
If a shutdown or button press is not performed within the specified time, the mode change is canceled. If update commands are executed in parallel, both will be cancelled.
The available properties include options such as “container”, “fetch”, “scheduler”, “traffic-gen”, “ipsec”, “pptp”, among others.
The “activation-timeout” property sets the time to activate the reset button or turn off the device.
You can also enable or disable the “flagged” state that indicates a possible intrusion.
[admin@MikroTik] > system/device-mode/print
mode: enterprise
flagged: yes
Sniffer: No.
hotspot: no
Specific changes can be made for each feature controlled by device-mode. For example, change “home” mode and enable email:
[admin@MikroTik] > system/device-mode/update mode=home email=yes
RouterOS scans the configuration at startup to detect intrusions. If a suspicious configuration is detected, it is disabled and set to a “flagged” state.
This imposes limitations, and certain actions, such as bandwidth testing or traffic generation, are not allowed.
[admin@MikroTik] > system/device-mode/print
mode: enterprise
flagged: yes
Sniffer: No.
hotspot: no
To exit the “flagged” state, use the command “/system/device-mode/update flagged=no”. It is crucial to audit the configuration before exiting the flagged state to ensure system integrity.
The “Device-mode” in MikroTik RouterOS provides an additional layer of security and customization, allowing network administrators to set specific limitations and detect intrusions.
By understanding how it works and how to apply specific settings, users can strengthen the security of their MikroTik devices and maintain finer control over enabled features.
Study material for the MTCNA Certification Course, updated to RouterOS v7
Study material for the MTCNA Certification Course, updated to RouterOS v7
Av. Juan T. Marengo and J. Orrantia
Professional Center Building, Office 507
Guayaquil. Ecuador
Zip Code 090505
to our weekly newsletters
Copyright © 2024 abcxperts.com – All Rights Reserved
40% discount on MikroTik books and book packs - Discount Code: AN24-LIB Discard
Take advantage of the Three Kings Day discount code!
Take advantage of the New Year's Eve discount code!
Take advantage of the discount code for Christmas!!!
all MikroTik OnLine courses
all Academy courses
all MikroTik Books and Book Packs
Take advantage of the discount codes for Cyber Week!!!
all MikroTik OnLine courses
all Academy courses
all MikroTik Books and Book Packs
Take advantage of the discount codes for Black Friday!!!
**Codes are applied in the shopping cart
Take advantage of discount codes for Halloween.
Codes are applied in the shopping cart
11% discount on all MikroTik OnLine courses
11%
30% discount on all Academy courses
30%
25% discount on all MikroTik Books and Book Packs
25%