(Book) Networking with MikroTik RouterOS: A Practical Approach to Understanding and Implementing RouterOS
Study material for the MTCNA Certification Course, updated to RouterOS v7
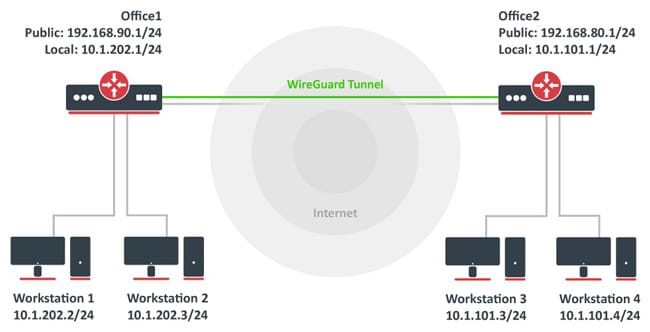
One of the newest and most promising VPN technologies is wire guard, which has gained recognition for its simplicity and efficiency compared to traditional solutions. MikroTik RouterOS Incorporates support for WireGuard, making it easier to implement this technology in a variety of scenarios.
At the end of the article you will find a small test that will allow you assess the knowledge acquired in this reading
WireGuard is a relatively new, open source VPN tunneling protocol that has become very popular in recent years due to its simplicity and efficiency. It was designed with a focus on ease of setup and maintenance, as well as superior performance compared to older VPN technologies such as IPsec and OpenVPN.
Deploying WireGuard on MikroTik RouterOS via the command line interface (CLI) can be done by following these basic steps.
This example provides a simple configuration to establish a VPN tunnel between a WireGuard server on MikroTik and a remote client. Remember to adapt specific settings, such as IP addresses and keys, to your own environment.
Make sure your MikroTik device is updated and supports WireGuard. To do this, you can check and update your version of RouterOS from the “System” and “Packages” menu in WinBox or through the CLI with the command /system package update check-for-updates and then /system package update install.
Generates a key pair (public and private) for the server and client. On the MikroTik device (server), use the following command to generate the keys:
/tool wireguard key generate
/tool wireguard key print
Configure the WireGuard interface on the MikroTik server with the generated private key and define a listening port. Replaces GENERATED-PRIVATE-KEY with your real private key.
/interface wireguard add name=wg0 listen-port=51820 private-key=GENERATED-PRIVATE-KEY
Adds the client device as a peer on the server, specifying the client's public key and the IP address to be assigned to the client within the VPN tunnel. Replaces CLIENT-PUBLIC-KEY with the client's real public key and CLIENT-IP with the desired IP address for the client within the VPN.
/interface wireguard peers add interface=wg0 public-key=CLIENT-PUBLIC-KEY allowed-address=CLIENT-IP/32
Assign an IP address to the WireGuard interface on the server and configure the necessary routes. For example, if you want the server to have the address 10.0.0.1 inside the VPN tunnel:
/ip address add address=10.0.0.1/24 interface=wg0
Configure routes if necessary, depending on your network and how you want traffic to flow through the VPN tunnel.
Make sure to allow UDP traffic for the WireGuard port (default, 51820) on the MikroTik firewall:
/ip firewall filter add action=accept chain=input protocol=udp port=51820
On the client device, you will need to perform a similar configuration, including creating a WireGuard interface, generating keys (if not already done), and configuring this interface with the client's private key and specifying the MikroTik server as your peer with the server's public key.
Remember that each environment is unique, and these steps may require adaptations. Additionally, it's always important to consider security and privacy when setting up VPNs, ensuring only authorized devices can connect.
Implementing WireGuard on MikroTik RouterOS offers numerous benefits, including:
WireGuard on MikroTik RouterOS adapts to a wide variety of scenarios, including:
WireGuard on MikroTik RouterOS is a modern, secure and efficient VPN solution that makes it easy to create virtual private networks. Its simple design, high performance, and strong security make it an attractive choice for a wide variety of applications, from enterprise networks to individual user remote access.
If you value simplicity, efficiency, and security in your VPN solutions, WireGuard on MikroTik RouterOS is an option you should definitely consider.
Study material for the MTCNA Certification Course, updated to RouterOS v7
Study material for the MTCRE Certification Course, updated to RouterOS v7
Av. Juan T. Marengo and J. Orrantia
Professional Center Building, Office 507
Guayaquil. Ecuador
Zip Code 090505
to our weekly newsletters
Copyright © 2024 abcxperts.com – All Rights Reserved
40% discount on MikroTik books and book packs - Discount Code: AN24-LIB Discard
Take advantage of the Three Kings Day discount code!
Take advantage of the New Year's Eve discount code!
Take advantage of the discount code for Christmas!!!
all MikroTik OnLine courses
all Academy courses
all MikroTik Books and Book Packs
Take advantage of the discount codes for Cyber Week!!!
all MikroTik OnLine courses
all Academy courses
all MikroTik Books and Book Packs
Take advantage of the discount codes for Black Friday!!!
**Codes are applied in the shopping cart
Take advantage of discount codes for Halloween.
Codes are applied in the shopping cart
11% discount on all MikroTik OnLine courses
11%
30% discount on all Academy courses
30%
25% discount on all MikroTik Books and Book Packs
25%