RouterOS v7 Advanced Security Book
Study material for the MTCSE Certification Course, updated to RouterOS v7
El Internet Control Message Protocol (ICMP) is a network layer protocol used to send control and error messages between devices on a network.
ICMP is an important protocol for the functioning of the Internet and is used for a variety of purposes, including:
At the end of the article you will find a small test that will allow you assess the knowledge acquired in this reading
ICMP is used to detect errors in data transmission. For example, if an IP packet is lost or corrupted, the sender can send an ICMP message to the recipient to inform them of the error.
ICMP is used to diagnose network problems. For example, you can use the “ping” command to send an ICMP message to a remote device to check if it is available.
ICMP is used for network management. For example, it can be used to send status notifications or to configure network devices.
ICMP is based on the IP protocol and uses the same headers as IP. The ICMP header has a type field that identifies the type of ICMP message.
There are many different types of ICMP messages, each serving a different purpose. Some of the most common ICMP message types include:
These messages are used to verify the availability of a remote device.
These messages are used to inform the sender that an IP packet could not be delivered to the destination.
These messages are used to inform the sender that an IP packet took too long to reach its destination.
ICMP is an important protocol for the functioning of the Internet. By understanding the concept of ICMP, you can help keep your network secure and functional.
Having an ICMP filter on the MikroTik RouterOS firewall is important for several reasons, including:
Here are some specific examples of how an ICMP filter in MikroTik RouterOS can help you protect your network:
It is important to configure the ICMP filter appropriately so that it does not block legitimate traffic. You should consider your specific needs and the security risks your network is exposed to.
On MikroTik routers with RouterOS, you can manage ICMP (Internet Control Message Protocol) related settings, including ping settings and other related functions.
ICMPv4 Message | Source from Device | Through Device | Destined to Device |
ICMPv4-unreach-net | Rate Limit | Rate Limit | Rate Limit |
ICMPv4-unreach-host | Rate Limit | Rate Limit | Rate Limit |
ICMPv4-unreach-proto | Rate Limit | Deny | Rate Limit |
ICMPv4-unreach-port | Rate Limit | Deny | Rate Limit |
ICMPv4-unreach-frag-needed | Send | permit | Rate Limit |
ICMPv4-unreach-src-route | Rate Limit | Deny | Rate Limit |
ICMPv4-unreach-net-unknown (Depr) | Deny | Deny | Deny |
ICMPv4-unreach-host-unknown | Rate Limit | Deny | ignore |
ICMPv4-unreach-host-isolated (Depr) | Deny | Deny | Deny |
ICMPv4-unreach-net-tos | Rate Limit | Deny | Rate Limit |
ICMPv4-unreach-host-tos | Rate Limit | Deny | Rate Limit |
ICMPv4-unreach-admin | Rate Limit | Rate Limit | Rate Limit |
ICMPv4-unreach-prec-violation | Rate Limit | Deny | Rate Limit |
ICMPv4-unreach-prec-cutoff | Rate Limit | Deny | Rate Limit |
ICMPv4-quench | Deny | Deny | Deny |
ICMPv4-redirect-net | Rate Limit | Deny | Rate Limit |
ICMPv4-redirect-host | Rate Limit | Deny | Rate Limit |
ICMPv4-redirect-tos-net | Rate Limit | Deny | Rate Limit |
ICMPv4-redirect-tos-host | Rate Limit | permit | Rate Limit |
ICMPv4-timed-ttl | Rate Limit | permit | Rate Limit |
ICMPv4-timed-reass | Rate Limit | permit | Rate Limit |
ICMPv4-parameter-pointer | Rate Limit | Deny | Rate Limit |
ICMPv4-option-missing | Rate Limit | Deny | Rate Limit |
ICMPv4-req-echo-message | Rate Limit | permit | Rate Limit |
ICMPv4-req-echo-reply | Rate Limit | permit | Rate Limit |
ICMPv4-req-router-sol | Rate Limit | Deny | Rate Limit |
ICMPv4-req-router-adv | Rate Limit | Deny | Rate Limit |
ICMPv4-req-timestamp-message | Rate Limit | Deny | Rate Limit |
ICMPv4-req-timestamp-reply | Rate Limit | Deny | Rate Limit |
ICMPv4-info-message (Depr) | Deny | Deny | Deny |
ICMPv4-info-reply (Depr) | Deny | Deny | Deny |
ICMPv4-mask-request | Rate Limit | Deny | Rate Limit |
ICMPv4-mask-reply | Rate Limit | Deny | Rate Limit |
The following ICMP rules are the types of messages that should generally always be available:
/ip firewall filter
add action=jump chain=forward jump-target=icmp
add action=accept chain=icmp comment="echo reply" icmp-options=0:0 protocol=icmp
add action=accept chain=icmp comment="net unreachable" icmp-options=3:0 protocol=icmp
add action=accept chain=icmp comment="host unreachable" icmp-options=3:1 protocol=icmp
add action=accept chain=icmp comment="host unreachable fragmentation required" icmp-options=3:4 protocol=icmp
add action=accept chain=icmp comment="allow source quench" icmp-options=4:0 protocol=icmp
add action=accept chain=icmp comment="allow echo request" icmp-options=8:0 protocol=icmp
add action=accept chain=icmp comment="allow time exceed" icmp-options=11:0 protocol=icmp
add action=accept chain=icmp comment="allow parameter bad" icmp-options=12:0 protocol=icmp
add action=drop chain=icmp comment="deny all other types"
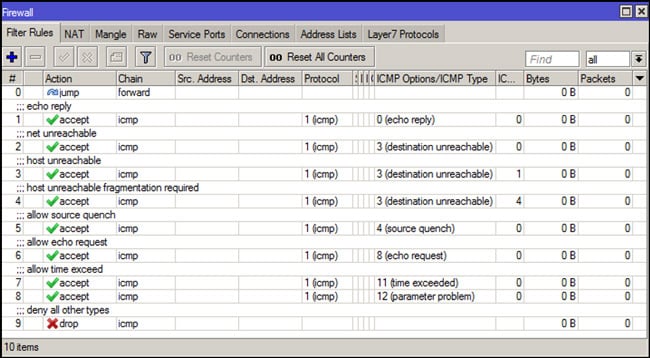
These are just examples and it is important to adapt the configuration according to your specific needs and network topology.
Remember to be careful when limiting ICMP traffic, as it can affect the network's diagnostic capabilities.
Be sure to test and validate any changes in a test environment before deploying them to a production environment.
Study material for the MTCSE Certification Course, updated to RouterOS v7
Av. Juan T. Marengo and J. Orrantia
Professional Center Building, Office 507
Guayaquil. Ecuador
Zip Code 090505
to our weekly newsletters
Copyright © 2024 abcxperts.com – All Rights Reserved
Take advantage of the Three Kings Day discount code!
Take advantage of the New Year's Eve discount code!
Take advantage of the discount code for Christmas!!!
all MikroTik OnLine courses
all Academy courses
all MikroTik Books and Book Packs
Take advantage of the discount codes for Cyber Week!!!
all MikroTik OnLine courses
all Academy courses
all MikroTik Books and Book Packs
Take advantage of the discount codes for Black Friday!!!
**Codes are applied in the shopping cart
Take advantage of discount codes for Halloween.
Codes are applied in the shopping cart
11% discount on all MikroTik OnLine courses
11%
30% discount on all Academy courses
30%
25% discount on all MikroTik Books and Book Packs
25%