RouterOS v7 Advanced Security Book
Study material for the MTCSE Certification Course, updated to RouterOS v7
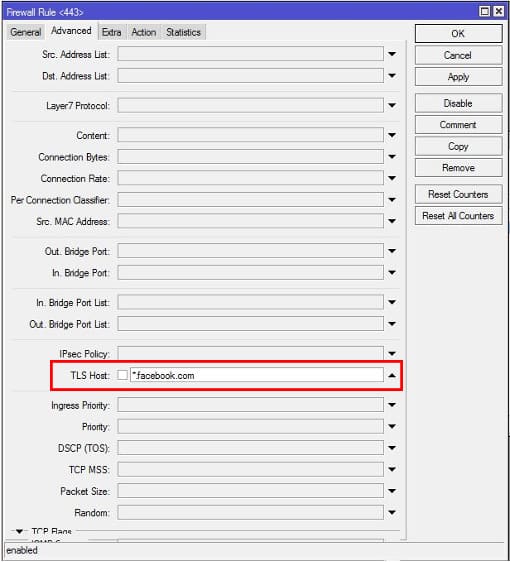
La tls-host option in MikroTik RouterOS is a firewall feature that allows TLS traffic to be filtered based on the domain name of the server it is directed to.
This can be useful for blocking access to malicious or unwanted websites, or for controlling the flow of traffic on your network.
At the end of the article you will find a small test that will allow you assess the knowledge acquired in this reading
However, it is important to note that using tls-host has some limitations and precautions:
The tls-host option can be a useful tool for filtering TLS traffic in MikroTik RouterOS, but it is important to use it with caution and be aware of its limitations.
Consider alternatives and follow appropriate security practices to protect your network effectively.
Most websites now use https and blocking https websites is much more difficult with MikroTik RouterOS version lower than 6.41. But starting with RouterOS v6.41, MikroTik Firewall introduces a new property called TLS Hos t which is able to match https websites very easily.
Therefore, blocking https websites like Facebook, YouTube, etc. It can be easily done with MikroTik Router if the RouterOS version is higher than 6.41.
You can use “tls-host” in firewall rules to filter traffic based on hostnames instead of IP addresses. This can be beneficial if the IP addresses of the servers you communicate with are prone to changing and you prefer to use hostnames that remain constant.
/ip firewall filter add chain=forward dst-port=443 protocol=tcp tls-host=example.com action=accept
In this example, the rule will allow outbound TLS traffic to port 443 destined for “example.com.”
By using the “tls-host” option, you can make it easier to manage SSL/TLS certificates on your network. If the certificates change or are renewed and the hostname remains the same, you will not need to update the firewall rules with new IP addresses.
In some cases, especially when interacting with cloud-hosted services or with service providers that may change assigned IP addresses, using “tls-host” provides an abstraction layer that reduces reliance on fixed IP addresses.
/ip firewall filter add chain=forward dst-port=8443 protocol=tcp tls-host=cloud-service.com action=accept
Here, outgoing TLS traffic to port 8443 destined for “cloud-service.com” will be allowed regardless of the current IP address of the service.
It is important to note that for the “tls-host” option to be effective, the remote service must support the use of host names instead of IP addresses. Not all services or applications allow this flexibility, so it is crucial to review the documentation for the specific service you are using.
/ip firewall filter add chain=forward dst-port=443 protocol=tcp tls-host=*.facebook.com action=drop
Study material for the MTCSE Certification Course, updated to RouterOS v7
Av. Juan T. Marengo and J. Orrantia
Professional Center Building, Office 507
Guayaquil. Ecuador
Zip Code 090505
to our weekly newsletters
Copyright © 2024 abcxperts.com – All Rights Reserved
Take advantage of the Three Kings Day discount code!
Take advantage of the New Year's Eve discount code!
Take advantage of the discount code for Christmas!!!
all MikroTik OnLine courses
all Academy courses
all MikroTik Books and Book Packs
Take advantage of the discount codes for Cyber Week!!!
all MikroTik OnLine courses
all Academy courses
all MikroTik Books and Book Packs
Take advantage of the discount codes for Black Friday!!!
**Codes are applied in the shopping cart
Take advantage of discount codes for Halloween.
Codes are applied in the shopping cart
11% discount on all MikroTik OnLine courses
11%
30% discount on all Academy courses
30%
25% discount on all MikroTik Books and Book Packs
25%