RouterOS v7 Advanced Security Book
Study material for the MTCSE Certification Course, updated to RouterOS v7
At Mikrotik, the tunnel mode and transport mode They are two different modes of operation for IPsec VPN connections.
At the end of the article you will find a small test that will allow you assess the knowledge acquired in this reading
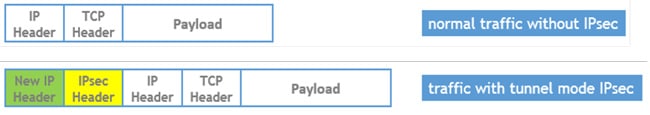
In tunnel mode, all traffic passing through the VPN interface is encapsulated in an IPsec packet. This means that traffic is encrypted and decrypted on both ends of the VPN connection.
Tunnel mode is the most secure configuration for VPN connections, as it protects all traffic, regardless of its protocol or application. However, it is also the most resource-demanding configuration, as it requires all packets to be encapsulated and decapsulated. In this mode the entire IP packet is encrypted and becomes the data component of a new (and larger) IP packet.
Frequently used in an Ipsec site-to-site VPN
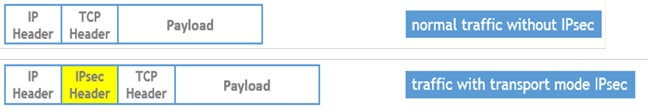
In transport mode, only data that is transmitted between two specific hosts is encapsulated in an IPsec packet. This means that traffic that is not directed to specific hosts is not encrypted or decrypted.
Transport mode is less secure than tunnel mode, as it does not protect all traffic. However, it is also less demanding in terms of resources, as it only requires that packets be encapsulated and deencapsulated when transmitted between specific hosts.
Frequently used for remote access VPNs
The following table summarizes the key differences between tunnel mode and transport mode:
Feature | tunnel mode | mode of transport |
Security | High | Low |
Resource requirement | High | Low |
Encapsulation | All traffic | Only traffic between specific hosts |
Choosing the correct mode for an IPsec VPN connection depends on the security and performance needs of the application.
If security is the top priority, tunnel mode is the best option. If performance is the main priority, transport mode is a good option.
In general, tunnel mode is the best choice for VPN connections that require a high level of security, such as connections used to access sensitive data. Transport mode is a good choice for VPN connections that require good performance, such as connections used to transmit high-speed data.
Tunnel type | Description |
Site-to-Site IPsec Tunnel | Securely connect two separate networks over the Internet. Allows secure communication between the subnets of the two locations. |
Remote Access IPsec VPN | Allows remote users to securely connect to the office network from external locations. It uses IPsec to secure the connection and can be implemented with different VPN protocols such as L2TP/IPsec or IKEv2/IPsec. |
L2TP/IPsec tunnel | Combines L2TP (Layer 2 Tunneling Protocol) with IPsec to create a secure tunnel. Often used for remote access connections. |
IKEv2/IPsec tunnel | It uses the IKEv2 (Internet Key Exchange version 2) protocol for security and key exchange, combined with IPsec for data protection. It offers a more efficient and robust configuration compared to IKEv1. |
EoIP/IPsec tunnel | It allows the creation of an Ethernet over IP (EoIP) tunnel and is then secured using IPsec to provide security. Useful for extending an Ethernet network over the Internet safely. |
IPIP | It allows the creation of an IPIP and is then secured using IPsec to provide security. |
All IPsec tunnels in MikroTik use the following elements:
The type of IPsec tunnel to choose depends on the specific needs of the application.
Study material for the MTCSE Certification Course, updated to RouterOS v7
Av. Juan T. Marengo and J. Orrantia
Professional Center Building, Office 507
Guayaquil. Ecuador
Zip Code 090505
to our weekly newsletters
Copyright © 2024 abcxperts.com – All Rights Reserved
40% discount on MikroTik books and book packs - Discount Code: AN24-LIB Discard
Take advantage of the Three Kings Day discount code!
Take advantage of the New Year's Eve discount code!
Take advantage of the discount code for Christmas!!!
all MikroTik OnLine courses
all Academy courses
all MikroTik Books and Book Packs
Take advantage of the discount codes for Cyber Week!!!
all MikroTik OnLine courses
all Academy courses
all MikroTik Books and Book Packs
Take advantage of the discount codes for Black Friday!!!
**Codes are applied in the shopping cart
Take advantage of discount codes for Halloween.
Codes are applied in the shopping cart
11% discount on all MikroTik OnLine courses
11%
30% discount on all Academy courses
30%
25% discount on all MikroTik Books and Book Packs
25%