Guide to building an Advanced Firewall in IPv6
- ML-013 [ code. 8013 ]
Sign up to access the full tutorial and protect your network with confidence!
- Share the information about this course
Content and access to the Tutorial
Course content
This tutorial includes
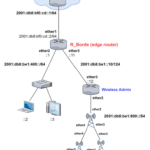
- Logical diagrams of the networks analyzed in the laboratories
- Detailed script of the different configurations
- Permanent access to the training portal
- Access to all future content updates or corrections
What you need to access this tutorial
- Internet connection of at least 1 Mbps
- Laptop or desktop computer preferably
- Tablet or cell phone are an alternative
What the student will learn
By completing this tutorial, students will be able to:
- Configuring Firewall Rules for Router Protection
- Management of Specific Security Protocols
- Protection of Internal Traffic
- Identifying and Blocking Bogon and Invalid IP Addresses
- IPv6 Management and Network Security
- RAW Rules Implementation
- Configuring Legitimate Traffic Acceptance
- Best Security Practices in IPv6 Networks
Requirements
- Understand basic networking concepts, such as network types (LAN, WAN), network topologies, and OSI/TCP-IP models.
- Know the differences between public and private IP addresses, and how they are used in networks.
- Have knowledge of subnets, netmasks and IP addressing.
- Understand the basic concepts of routing and switching in networks.
- Know how Dynamic Host Configuration Protocol (DHCP) and Domain Name System (DNS) work.
- Understand the assignment of dynamic and static IPs.
General Purpose
Equip students with the knowledge and skills necessary to design, implement and manage an advanced firewall in IPv6 environments, using MikroTik RouterOS.
Through this tutorial, participants will learn how to efficiently protect their networks, controlling incoming and outgoing traffic and ensuring the integrity of data and the availability of services on the network.
Objectives by Chapter
1. Configure Input Rules for Router Protection
Teach students to configure firewall rules in the input chain to safeguard the router from unauthorized access and external attacks.
- Allow UDP traceroute, DHCPv6 client PD, and IPSec (IKE, AH, ESP) to ensure the connectivity and protection necessary for the operation of the router.
2. Configure Forward Rules to Protect Customer Traffic
Guide students in creating forward rules to protect the internal network, filtering harmful or unsolicited traffic before it reaches client devices.
- Implement rules for IPSec (IKE, AH, ESP) for secure traffic through the router.
- Discard incorrect IP addresses and packets with Hop Limit=1 to improve network security.
3. Configure RAW Rules for Bogon IPs
Provide knowledge on how to configure rules on the RAW table to prevent attacks from networks and IP addresses known to be sources of malicious traffic.
- Configuration to discard Bogon IPs and packets from invalid IPs.
- Filters to discard non-routable global IPv6 addresses.
- Allow all legitimate traffic from the WAN to the LAN to maintain internal network functionality without compromising security.
At the end of this Tutorial
Upon completion of this tutorial, students will be able to:
- Design and implement a robust set of firewall rules in MikroTik RouterOS that effectively protects devices and the network against external threats, using the advanced capabilities of IPv6.
- Understand and apply best practices for managing incoming and outgoing traffic, ensuring that only legitimate and secure traffic can pass through the router.
- Identify and mitigate Possible network vulnerabilities by filtering malicious or unwanted traffic, including Bogon addresses, invalid IPs, and non-routable IPv6 traffic.
- Ensure connectivity and secure communication within the network through the correct implementation of specific rules for protocols such as IPSec.
- win a solid understanding how to configure firewall rules in the input, forward and RAW contexts, offering comprehensive protection in an IPv6 environment.
This advanced knowledge in IPv6 network security will allow students to not only protect their own networks, but also offer consulting and technical support services to other organizations seeking to improve the security of their network infrastructures with MikroTik RouterOS.