Switching and Bridging RouterOS v7 Book
Study material for the MTCSWE Certification Course updated to RouterOS v7
VLAN Trunking It is an essential function in network administration, and the protocol IEEE 802.1Q It is the standard that defines how it is implemented. Understanding these concepts is essential to effectively manage a network.
At the end of the article you will find a small test that will allow you assess the knowledge acquired in this reading
Before going into details, it is important to understand some fundamental concepts.
VLAN is the abbreviation of Virtual Local Area Network. It refers to a group of network devices that behave as if they were on the same physical network, regardless of their actual physical location.
VLANs can help reduce network congestion, improve security, and facilitate network management.
In the context of networks, the trunking refers to the practice of transmitting multiple streams of information simultaneously over a single network link.
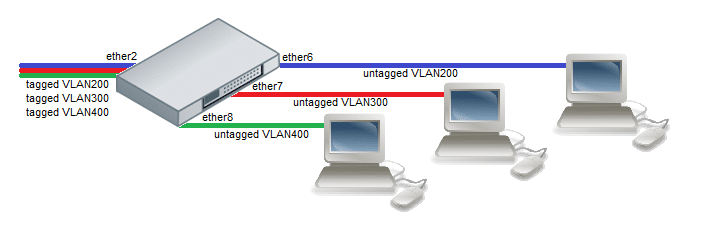
VLAN Trunking is a technique used to allow multiple VLANs to be transmitted over a single communication link. "trunk" o "trunk" between switches. This allows devices on different VLANs to communicate with each other, despite being on separate networks.
IEEE 802.1Q is the standard that defines how VLAN trunking is implemented in an Ethernet network. In short, it allows an Ethernet link to carry traffic from multiple VLANs by adding a “tag” to the Ethernet frames that identifies which VLAN a particular frame belongs to. This labeling process is known as “tagging”.
When a switch receives a frame from an access port (assigned to a specific VLAN), adds a 802.1Q label to the frame before sending it over the trunk link. This tag contains an identifier VLAN (VID) which specifies which VLAN the frame belongs to.
When the frame arrives at another switch over the trunk, it reads the 802.1Q tag to determine which VLAN the frame belongs to. Then, it removes the tag and sends the frame through the access port corresponding to the specified VLAN.
The main advantage of VLAN trunking is the efficiency. Enables data transmission from multiple VLANs over a single physical link, reducing the need for additional cabling and improving network performance.
Additionally, it makes network management easier by allowing network administrators to group network devices logically instead of physically.
However, VLAN trunking can also increase network complexity and requires careful planning to ensure that traffic is kept segregated where necessary and allowed where inter-VLAN communication is required.
Advantages | Disadvantages |
|---|---|
| Network efficiency: Trunking allows data transmission from multiple VLANs over a single physical link, reducing the need for additional cabling. | Complexity: Configuring and managing VLANs and trunking can be a complex process and require a high level of technical skill. |
| Security: VLANs can help improve security by isolating different types of traffic on different virtual networks. | Security risks: If not configured correctly, VLANs and trunking can introduce security risks, such as VLAN hopping. |
| Facilitates network administration: VLANs allow network devices to be grouped logically rather than physically, making network management easier. | Performance: If used incorrectly, trunking can lead to network performance problems such as congestion. |
| Scalability: With trunking, you can easily add more devices to a VLAN without the need for additional cabling. | Supplier dependency: Some VLAN and trunking features may be vendor-specific, which may limit network hardware options. |
When talking about 802.1Q and VLAN trunking, it is also important to mention the concept of “Native VLAN”. The native VLAN is the default VLAN that is assigned to a trunk. Frames that belong to the native VLAN are sent over the trunk without an 802.1Q tag.
The reason the native VLAN frames are not tagged is to allow compatibility with network devices that do not support 802.1Q. Therefore, if an untagged frame arrives on a trunk port, the switch will assume that the frame belongs to the native VLAN.
Although VLAN trunking with 802.1Q has its benefits, it also presents some security issues. One of these is the attack of VLAN hopping. In this type of attack, a malicious individual can send tagged frames to an access port of a switch in an attempt to access other VLANs over the trunk.
To mitigate this risk, it is a good security practice to disable VLAN trunking on all ports that connect to hosts, and only allow it on ports that connect to other switches. It is also advisable to change the native VLAN to a VLAN that is not used for any other purpose.
In addition to 802.1Q, Cisco It also has its own VLAN trunking protocol, called Dynamic Trunking Protocol (DTP). DTP allows automatic negotiation of trunking mode between two switches. Although DTP can simplify trunking configuration, it can also be a security vulnerability if not managed properly, as it can allow an attacker to configure an access port as a trunk port.
In conclusion, VLAN trunking and the IEEE 802.1Q protocol are fundamental aspects of modern network management. They allow efficient communication between different VLANs over a single network link, improving efficiency and flexibility. However, they also require careful management to ensure network security and avoid issues such as VLAN hopping.
Study material for the MTCSWE Certification Course updated to RouterOS v7
Av. Juan T. Marengo and J. Orrantia
Professional Center Building, Office 507
Guayaquil. Ecuador
Zip Code 090505
to our weekly newsletters
Copyright © 2024 abcxperts.com – All Rights Reserved
40% discount on MikroTik books and book packs - Discount Code: AN24-LIB Discard
Take advantage of the Three Kings Day discount code!
Take advantage of the New Year's Eve discount code!
Take advantage of the discount code for Christmas!!!
all MikroTik OnLine courses
all Academy courses
all MikroTik Books and Book Packs
Take advantage of the discount codes for Cyber Week!!!
all MikroTik OnLine courses
all Academy courses
all MikroTik Books and Book Packs
Take advantage of the discount codes for Black Friday!!!
**Codes are applied in the shopping cart
Take advantage of discount codes for Halloween.
Codes are applied in the shopping cart
11% discount on all MikroTik OnLine courses
11%
30% discount on all Academy courses
30%
25% discount on all MikroTik Books and Book Packs
25%